Qualys SSL Server Test is a tool that helps determine how secure the connection between the website and the browser really is.
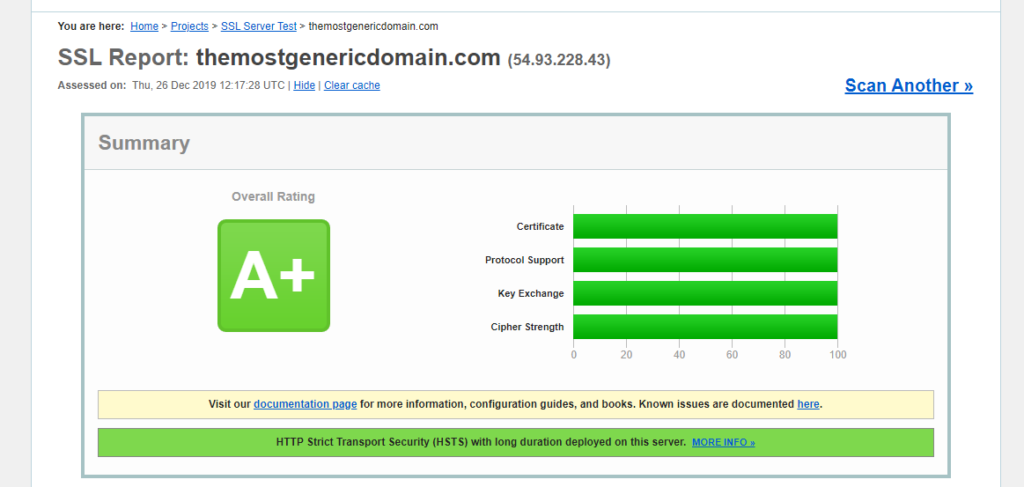
The process is easy: You just provide the domain name of the website and then (after 5 minutes of wait time), the tool will provide you with the results. The result page looks something like this:
On the results page, you will find the details regarding the following aspects:
- Certificates installed on the server
- Protocols and cipher suites in use
- Handshake Simulation Report
- Protocol Details Report
The final grade of the test is based on all of the factors mentioned above and here. The highest grade is “A+”, and the lowest one is “F”.
The test will also include the grading of each of the following parameters: Certificate, Protocol Support, Key Exchange algorithms, and Cipher Strength.
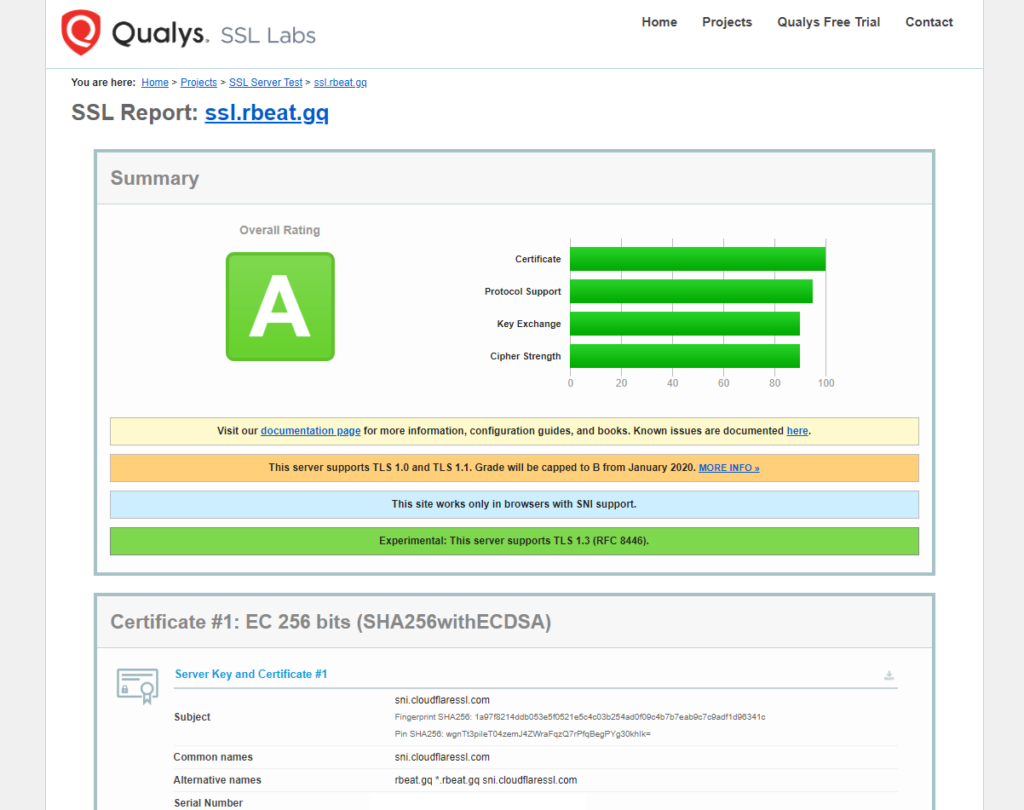
Here is an example of a website that has the highest rating possible:
Pay attention to the cipher suites being used on the server:

To achieve this grade, these steps were made:
- ECC Certificate was installed on the website. (Click here to check the guide on how to get one)
- Cipher suites with the encryption lower than 256-bits were disabled.
- All of the protocols (Except for TLS 1.2/1.3) were disabled.
- HSTS has been enabled on the server.
Here is how the configuration file on the server looks like (Apache):
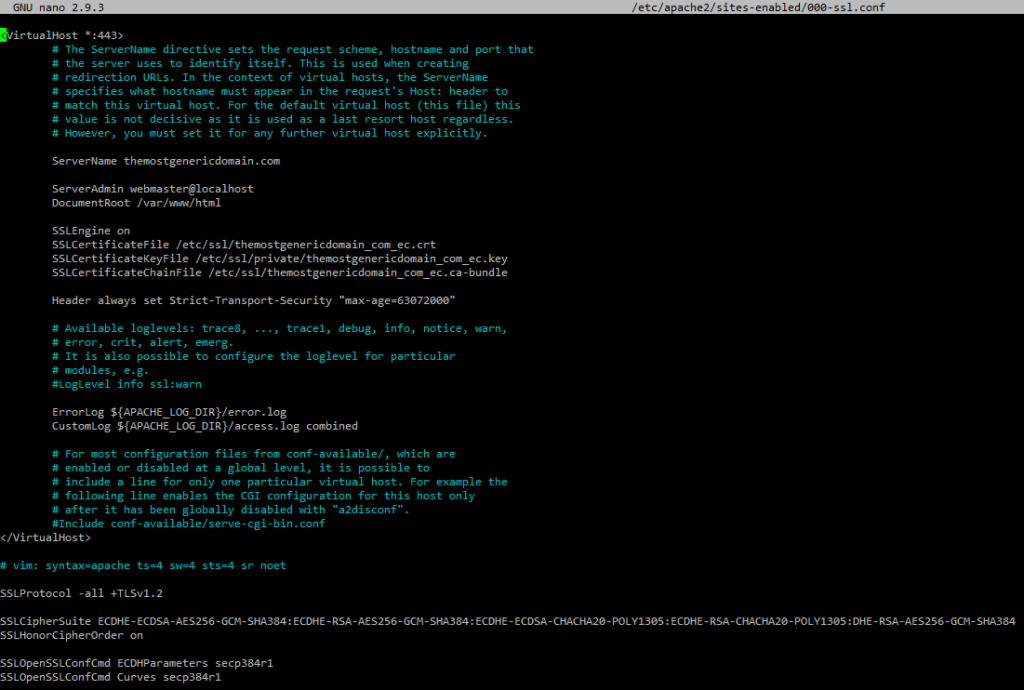
This version of Apache does not support TLS 1.3, that is why it was not enabled here.
As you can see, a lot of additional parameters were enabled to pass the test with the highest grade. They have made the website more secure; however, some of the clients (browsers) may experience issues while accessing the web-page. It can be seen here:
| Android 5.0.0 | Server sent fatal alert: handshake_failure |
| Chrome 49 / XP SP3 | Server sent fatal alert: handshake_failure |
| Firefox 31.3.0 ESR / Win 7 | Server sent fatal alert: handshake_failure |
| Safari 6 / iOS 6.0.1 | Server sent fatal alert: handshake_failure |
| Safari 7 / iOS 7.1 R | Server sent fatal alert: handshake_failure |
| Safari 7 / OS X 10.9 R | Server sent fatal alert: handshake_failure |
| Safari 8 / iOS 8.4 R | Server sent fatal alert: handshake_failure |
| Safari 8 / OS X 10.10 R | Server sent fatal alert: handshake_failure |
Unfortunately, these clients (OS and browsers) have failed to initiate the SSL Handshake with the server, since they do not the protocols allowed on the server.
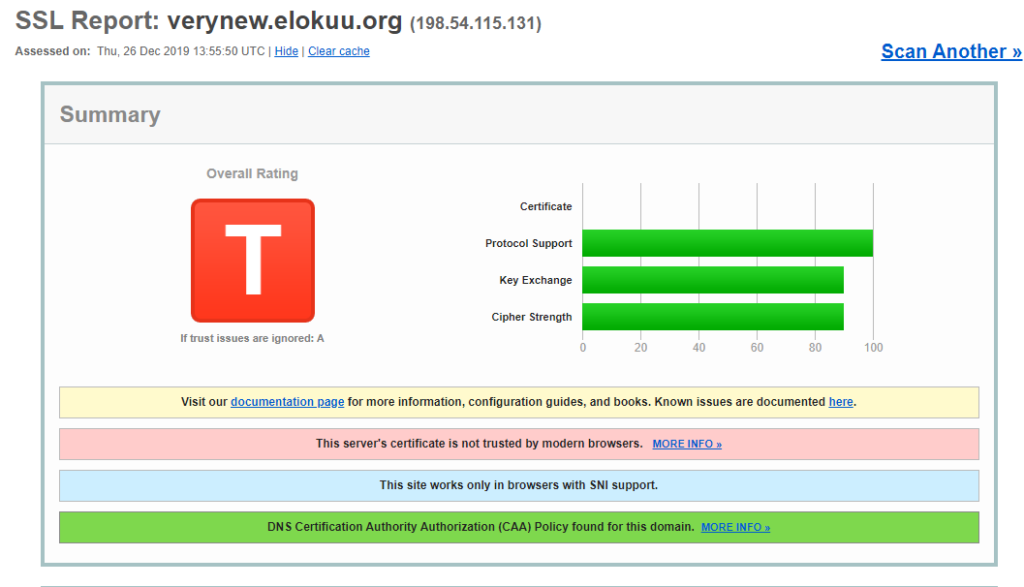
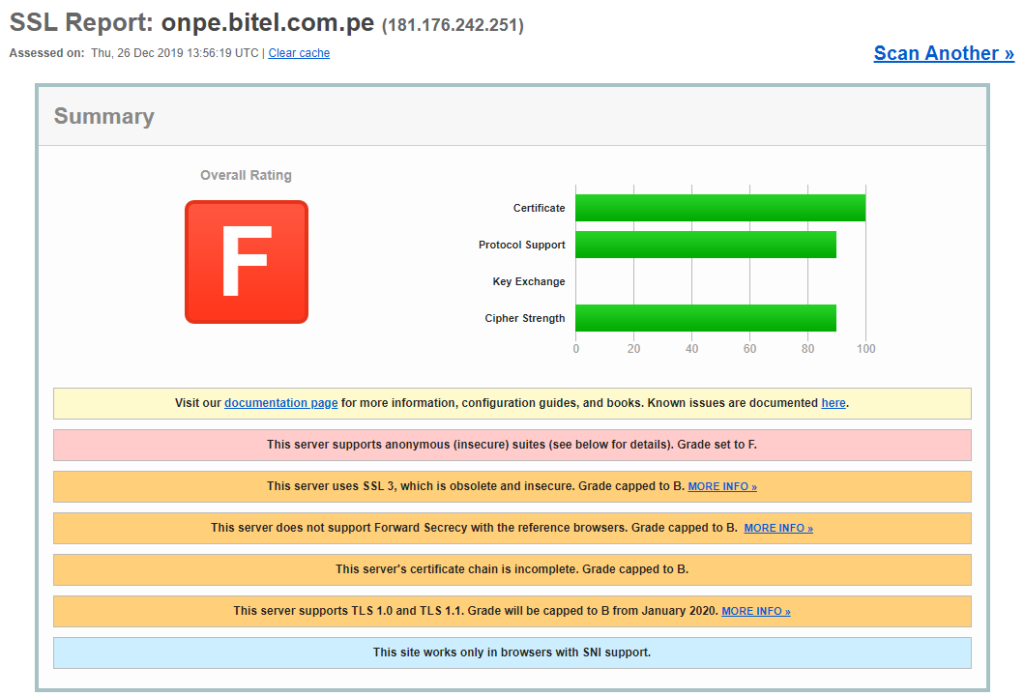
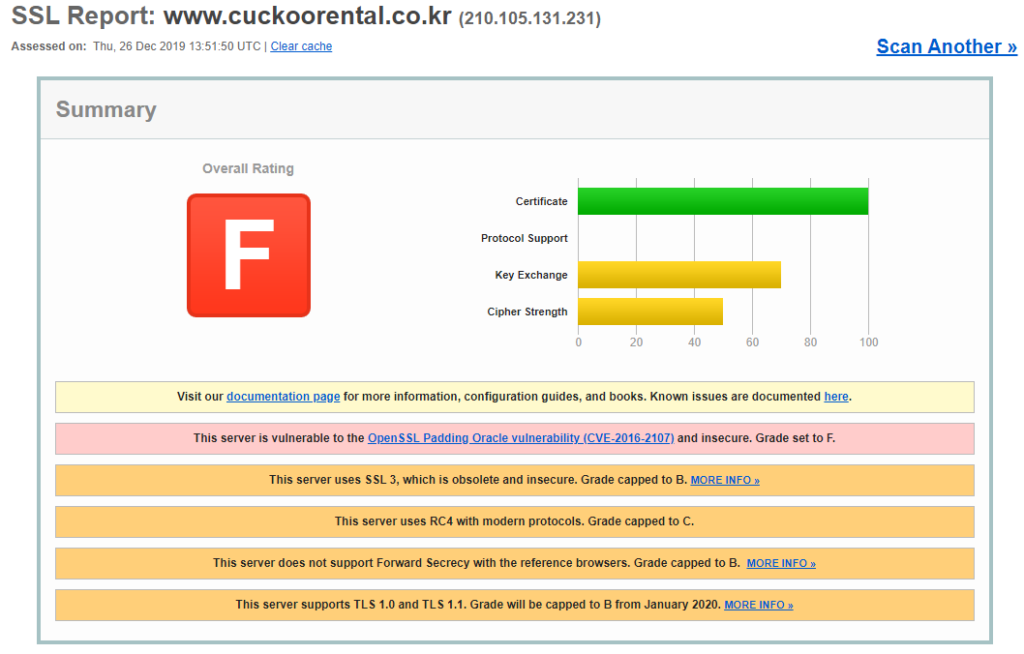
Bonus: (Worst graded websites)